USB devices such as the above (which come in more discrete versions) can go completely undetected while performing malicious operations on any machine with a USB port. Due to the ubiquitous nature of USB devices, we often pay little attention to their capabilities. This makes them an ideal candidate for cybercriminals.
At Hark, we use this to demonstrate the consequences of leaving an unlocked and unattended machine. Which will most likely result in a Justin Bieber wallpaper – Let’s face it, nobody wants that!
How it works
It’s comprised of two main components, the external storage, and the micro-controller.
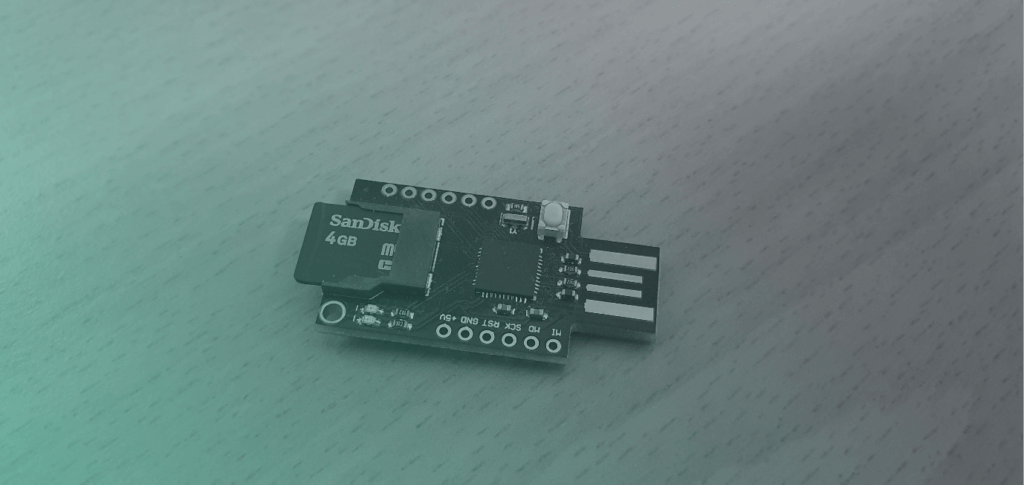
The external storage (SD card) acts as an instruction store. This allows for an easy interface to change or update the commands that are executed. On the other hand, the micro-controller (ATmega 32U4) is the brains of the operation. This communicates with your machine and presents itself as a HID (Human Input Device) which may be a mouse or a keyboard.
Once plugged in – the micro-controller will get to work and start reading and executing whatever commands have been instructed. For example; the instructions could be to send keystrokes to search for a command shell, wait a moment or two while it loads, then execute a series of actions.
What can it do?
When activated, these devices can create backdoors, download viruses/malware or even upload your data to a remote location. However, it is more likely that criminals would execute malicious software to spy on your activity, such as recording keystrokes and even viewing your webcam, long after the USB has been detached.
What can you do to prevent it?
For the most part, understanding how it works is all well and good, but I imagine you will want to know how you can go about preventing it, and the answer is simple. Already assuming you follow good security practices, you will likely have a strong password protected machine, meaning once your machine is locked, it requires you to enter a password to regain entry. If so, then that’s a great start, but this is only effective while locked. So, for whatever reason you must leave your machine unattended, it’s a good idea to get into the habit of also ensuring it’s locked.
A locked computer will deem any malicious keystrokes or mouse movements sent by the device useless, as it won’t have access to your logged-in account, thus not being able to open applications such as the command shell. However, this does not prevent you from plugging in those free, untrusted USB sticks, while logged in. So, watch out for that!
If you wish to take the security of your machine further, you could disable inactive USB ports or blacklist the automated device installation.
At Hark, we take device security very seriously, and the protection of customer data is a number one priority. As a result, our services are routinely penetration tested, as well as our security policies are continuously reviewed.
If you would like to find out more about how the Hark Platform can help, please get in touch.



